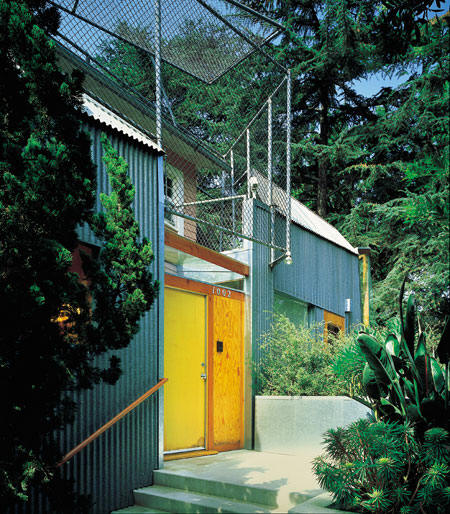
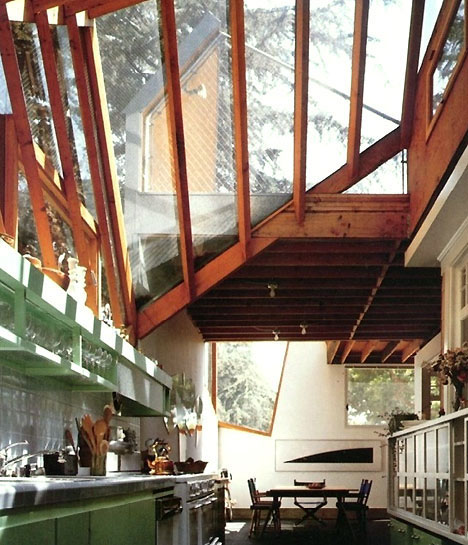
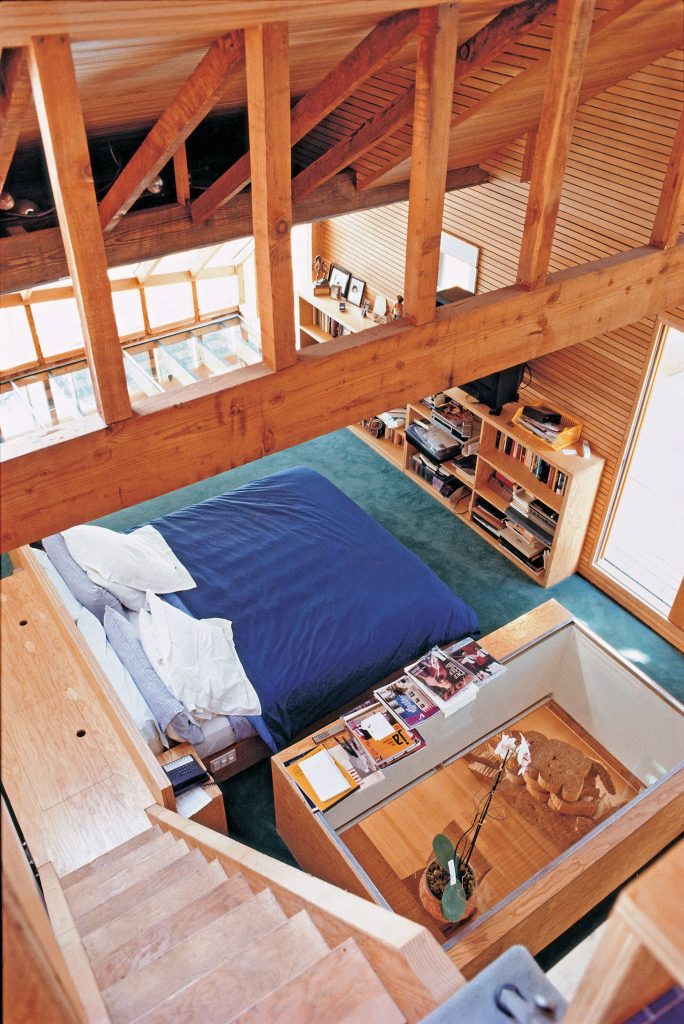
Gehry House
/
















This exploit involves accessing files and directories that are stored outside the web root folder by manipulating variables that reference files.
Beyond exploitation, the primary goal of Gruyere is to teach effective defense mechanisms. Google builds lessons for Web Application Security
Gruyere shows how attackers can manipulate client-side data, such as cookies, to escalate privileges or spoof other users. gruyere learn web application exploits defenses top
Google Gruyere is a hands-on codelab developed by Google to help developers and security enthusiasts learn about web application exploits and defenses. Built around a "cheesy" microblogging application written in Python, the course intentionally includes a wide range of security bugs to demonstrate how vulnerabilities occur and how to fix them. Core Exploits Taught in Gruyere
The course demonstrates how an attacker can trick a victim's browser into performing unauthorized actions on their behalf. This exploit involves accessing files and directories that
Users learn to find both reflected and stored XSS vulnerabilities by injecting scripts into input fields and URLs.
The lab teaches how simple bugs can lead to sensitive data exposure or application crashes. Key Defense Strategies Google Gruyere is a hands-on codelab developed by
The Gruyere codelab covers several critical vulnerability classes, many of which align with the OWASP Top 10 .